Since its inception 56 years ago, the Defense Advanced Research Projects Agency, essentially the U.S. Department of Defense’s mad scientist division, has turned fiction into fact and revolutionized our world several times over by thinking big and weird. They’ve invented the proto-internet, GPS systems, and even bent light itself to make 40 trillionths of a second disappear. They’re currently tinkering with laser guns, health monitoring internal nanobots, and virus-killing blood cleaning technology, just to name a few. But right now, one of DARPA’s main focuses is on something called the Active Authentication Project, launched in 2012 with the explicit and initially confounding mission of eliminating passwords as we know them, to better guard us all online.
DARPA isn’t coming out of left field. Up to 55 percent of security professionals think passwords are a fundamentally flawed means of protection, and it’s common knowledge that they’re easily poached by programs like Heartbleed—just this month, a group of Russian hackers amassed 1.2 billion internet credentials. Even long, complex passwords don’t seem to be protecting us well, and can be broken down by hacking systems. A decade ago, Bill Gates predicted passwords would die. Then, last year, several tech firms launched the Petition Against Passwords. Now a group called the FIDO Alliance hopes to do away with internet passwords altogether by 2015, although there’s no official consensus on how exactly to do this.
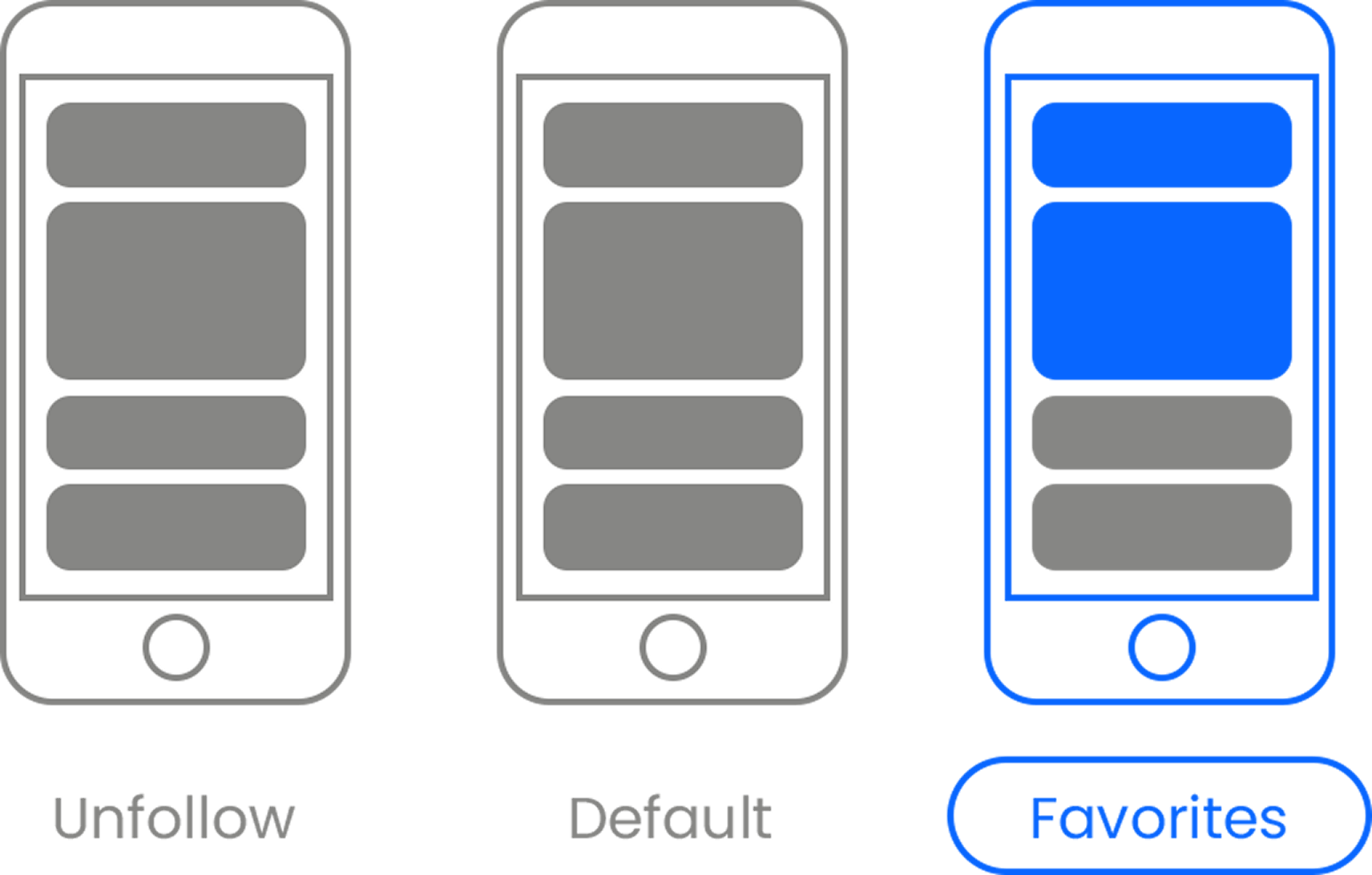
To date, many tech companies have sought to replace traditional passwords with things like knock code, multi-step verification, physical lock-and-key systems, and even biometrics. Google, a champion of multi-stage logins, recently acquired SlickLogin, a program that will transmit a near-silent sound from your computer to an app on your phone, which then returns a signal to a website server to confirm a user’s identity. Google is betting heavily on the elaborate technology, believing it to be one of the most effective and difficult to replicate multi-step verifications. And many phones now have basic finger (or even ear) scanning technology like the Ergo app, which provides greater individual specificity and security than fingerprints, which can still be lifted or easily smudged.
But all of these systems still have serious flaws. Even non-verbal codes can be broken, physical locks can be lost, and a multi-step process, in the end, only verifies safety at the sign-in stage, while threatening to screw over users who, in SlickLog’s case, for example, lose their phones. Mistake-free, multi-step verifications are invasive, like Google’s plan to have people ingest radio frequency-transmitting pills or wear electronic tattoos. As for biometrics, aside from being unreliable and easily fooled, many involve clunky lifestyle changes and new equipment like wristbands to monitor heart signals or special bio-soles to verify your identity by foot pressure. There have been attempts to make biometrics more discerning, with cameras that monitor the formation of facial expressions or finger sensors that can detect a user’s blood and oxygen flows.
DARPA’s push to end the password is a revolutionary, two-pronged (if borderline Orwellian) approach: First, they’re focusing on “cognitive fingerprints,” which track how a user moves or acts, identifying the individual not only at login, but continuously, throughout their experience. The method assesses subconscious or automatic factors like muscle movement, which are almost impossible to replicate. Second, DARPA is reinforcing the cognitive fingerprint process with existing technology, using the sensors and apps already on our computers and phones in unexpected ways. Partnering up with scientists from Drexel University, the NASA Jet Propulsion Laboratory, New York Institute of Technology, Southwest Research Institute, and SRI International, DARPA is working to detect our “authorial fingerprint,” based on writing style, speed, and errors. The organization aims to build detection techniques around the unique rhythms and electric signals of our hearts, the micro movements in our hands as we gesture, our patterns of response to randomly generated system error messages, and the speed, style, and balance of our stride and posture.
Progress is promising, but all of these technologies are still in the early stages of development. It will be a while before kinks are ironed out and developers make the login and constant verification process seamless and inoffensive. And, on DARPA’s end, it’s likely that the systems they develop will only make it to the public after first launching on Defense Department computers. For many of us, that’s actually cause for relief—even though the DARPA programs are a far cry from anything as invasive as swallowing a password pill á la Google’s one-time plan, they do involve storing a great deal of intensely personal data. But even if the current forms are disturbing, the mission is still worthwhile. Maybe we’ll reject some of the more intrusive options, but in an age of vulnerability and shrinking privacy, any meaningful step we take in the quest for personal security is a step in the right direction.














 Otis knew before they did.
Otis knew before they did.